Technical Overview of Wireless Networking, Security and Compliance
This is a summary of the technical concepts behind wireless networking as well as Security and Compliance of the EUI WiFi. Please note for specific information on using the wireless facility at the Institute, refer to Wireless Access at the EUI.
Wireless networking, also known as WLAN (Wireless Local Area Network), is a way to connect to a network by using radio frequencies.
WLAN architecture consists of three basic elements:
- Wired infrastructure: the existing wired LAN;
- Client systems: wireless capable mobile devices such as laptops, tablets and smartphones;
- Access Points (AP): the "bridges" that enable mobile devices to connect to the wired LAN infrastructure. They transmit and receive the radio signals and convert them into frames suitable for transport over the wired LAN.
The leading standard in Europe for wireless networking today is 802.11b/g/n, developed by the Institute of Electrical and Electronics Engineers (IEEE). Also known as Wi-Fi, this standard operates in the 2.4 GHz band:
- 802.11b allows a maximum bandwidth up to 11Mbps;
- 802.11g allows up to 54Mbps;
- 802.11n allows up to 300 Mbps in right conditions.
This translates into a speed which can result slower than a wired LAN connection which is thus always preferable whenever available.
It should be noted that the above maximum bandwidths cited are shared amongst all connected users. Hence, a single user would benefit from the full capacity, whereas 30 users concurrently attached to the same Access Point would notice degradation in performance.
The EUI wireless network infrastructure supports 802.11g and n standards.
One IEEE 802.11 AP can typically communicate with 30 client systems located within a radius of roughly 100m.
However, the actual range of communication can vary significantly, depending on such variables as indoor or outdoor placement, height above ground, nearby obstructions, other electronic devices that might actively interfere with the signal by broadcasting on the same frequency, type of antenna, the current weather, operating radio frequency, and the power output of devices.
The range of APs can be extended by network designers through the use of repeaters and reflectors, which can bounce or amplify radio signals that ordinarily would go un-received.
The power of a device is determined in dBm which is an abbreviation for the power ratio in decibels (dB) of the measured power referenced to one milliwatt (mW).
The signal quality of the network is measured in RSSI (Radio (Received) Signal Strength Indicator) which is usually expressed in units of decibel (dB) or the similar dBm (dB per milliwatt) in which the smaller magnitude negative numbers have the highest signal strength, or quality.
It can as well be represented by a percentage value between 0 and 100: value of 0 implies an actual RSSI signal strength of -100 dbm whereas a value of 100 implies an actual RSSI signal strength of -50 dbm.
On EUI's coverage maps scale, the unit used is the nanoWatt:
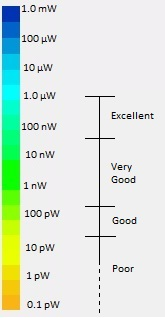
Figure 1: Signal quality in (nano)Watts
Roughly 200 Access Points are installed all over the Campus: a detailed map of their location as well as wifi network coverage and signal quality can be found here.
The Service Set IDentifier (SSID) is a network name for the devices in a WLAN system. The SSID prevents access from any client device that has not received the SSID itself.
Normally, an Access Point (AP) broadcasts its SSID in its beacon, such that it can be picked up by any client device within range.
The ICT broadcasts four different SSID's, each of which has a specific purpose: EUI-WiFi, EUI-Guest, EUIflats and eduroam (click here for further info).
The 802.11b/g/n standard supports different means of client authentication between the wireless client system and the AP:
- Open Key Authentication
- Shared Key Authentication
- 802.1x Authentication
Open Key Authentication does not require any user authentication in associating to the wireless network. Users only need to know the correct SSID details to associate to such a wireless network. There is no encryption for the data transmitted and received.
This is the case of the EUI-Guest wireless network where users can associate to the SSID without any authentication and their traffic is transmitted in clear while the big internet access is filtered by a portal.
With Share Key Authentication, the AP sends the client device a challenge text packet that the client must then encrypt with the correct key and return to the AP.
If the client has the wrong key or no key, authentication will fail and the client will not be allowed to associate with the AP. Shared key encrypts data transmitted and received.
The above authentication is implemented in the EUIflats wireless network.
802.1X Authentication standard provides WLANs with strong, mutual authentication between a client and an authentication server.
There are several 802.1X authentication types (LEAP, PEAP, etc.), each providing a different approach to authentication while relying on the same framework and the Extensible Authentication Protocol (EAP) for communication between a client and an AP.
With 802.1X authentication types such as PEAP with WPA2-Enterprise, mutual authentication is implemented between the client and a Remote Authentication Dial-In User Service (RADIUS) server. The credentials used for authentication, such as log-on password, are never transmitted in clear, or without encryption, over the wireless medium.
EUI-WiFi and eduroam wireless networks use Protected EAP (PEAP) 802.1X Authentication.
Wi-Fi Protected Access (WPA) and Wi-Fi Protected Access II (WPA2) are two sets of security protocols and security certification programs developed by the Wi-Fi Alliance to secure wireless computer networks.
WPA encrypts information and makes sure that the network security key has not been modified. Wi‑Fi Protected Access also authenticates users to help ensure that only authorized people can access the network.
WPA is designed to be used with an 802.1X authentication server (RADIUS), which distributes different keys to each user. This is referred to as WPA- or WPA2-Enterprise.
EUI-WiFi and eduroam wireless networks use WPA2-Enterprise along with AES encryption.
WLAN security at the EUI consists of a combination of the use of SSIDs along with different types of Authentication. These measures provide for access control and privacy.
To provide robust wireless security services that closely parallel the security available in a wired LAN, the ICT is implementing all of the following features:
- 802.1X authentication standards
- User and session authentication
- Access Point authentication
- Detection of rogue access points
- Unicast key management
- Client session accounting logs
- Mitigation of network attacks
- WLAN management
In radio communication systems, equivalent isotropically radiated power (EIRP) or, alternatively, effective isotropically radiated power, is the amount of power that a theoretical isotropic antenna (which evenly distributes power in all directions) would emit to produce the peak power density observed in the direction of maximum antenna gain.
EIRP can take into account the losses in transmission line and connectors and includes the gain of the antenna. The EIRP is often stated in terms of decibels per milliwat (dBmw) over a reference power emitted by an isotropic radiator with an equivalent signal strength.
The EIRP allows comparisons between different emitters regardless of type, size or form. From the EIRP, and with knowledge of a real antenna's gain, it is possible to calculate real power and field strength values.
The EIRP is used to estimate the service area of the transmitter, and to coordinate transmitters on the same frequency so that their coverage areas do not overlap. In built-up areas, regulations restrict the EIRP of a transmitter to prevent exposure of personnel to high power electromagnetic fields.
The Access Points installed at the EUI Campus are CISCO certified and respect the European directives 1999/5/EC & 93/42/ECC.
This compliance grants the respect of current European and Italian Laws in terms of emitted power and channel utilization for health safety.
Page last updated on 18 June 2025